Connecting Timely with Okta
Integrations Single Sign-On (SSO) Handbook Manage users and access all in one place using Okta single sign-on for Timely.Adding new users to Timely and managing their access has never been easier with our Okta single sign-on integration!
Set-up instructions
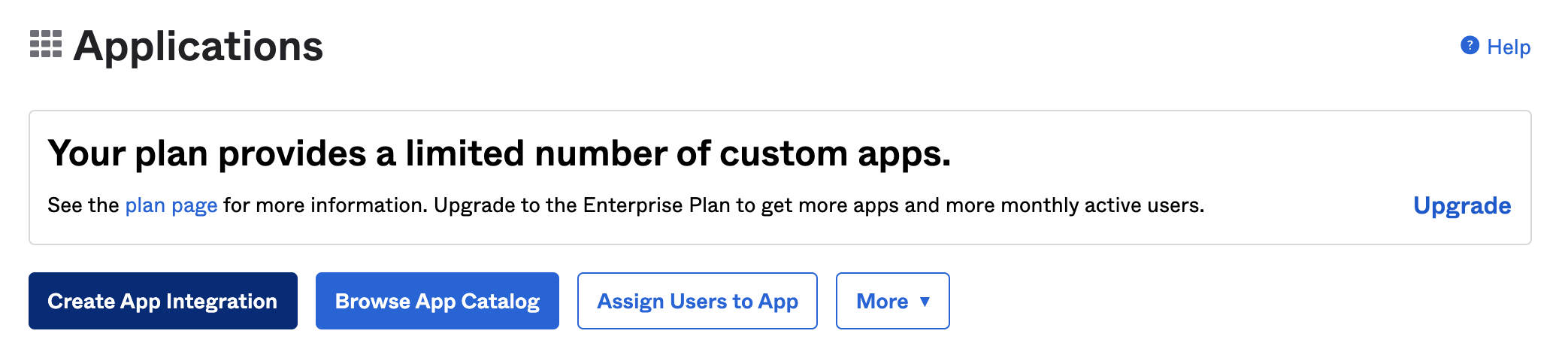
First, log into your Okta admin account and click on the Applications dropdown in the left-hand sidebar. Click Applications, then click the “Create app integration” button along the top.
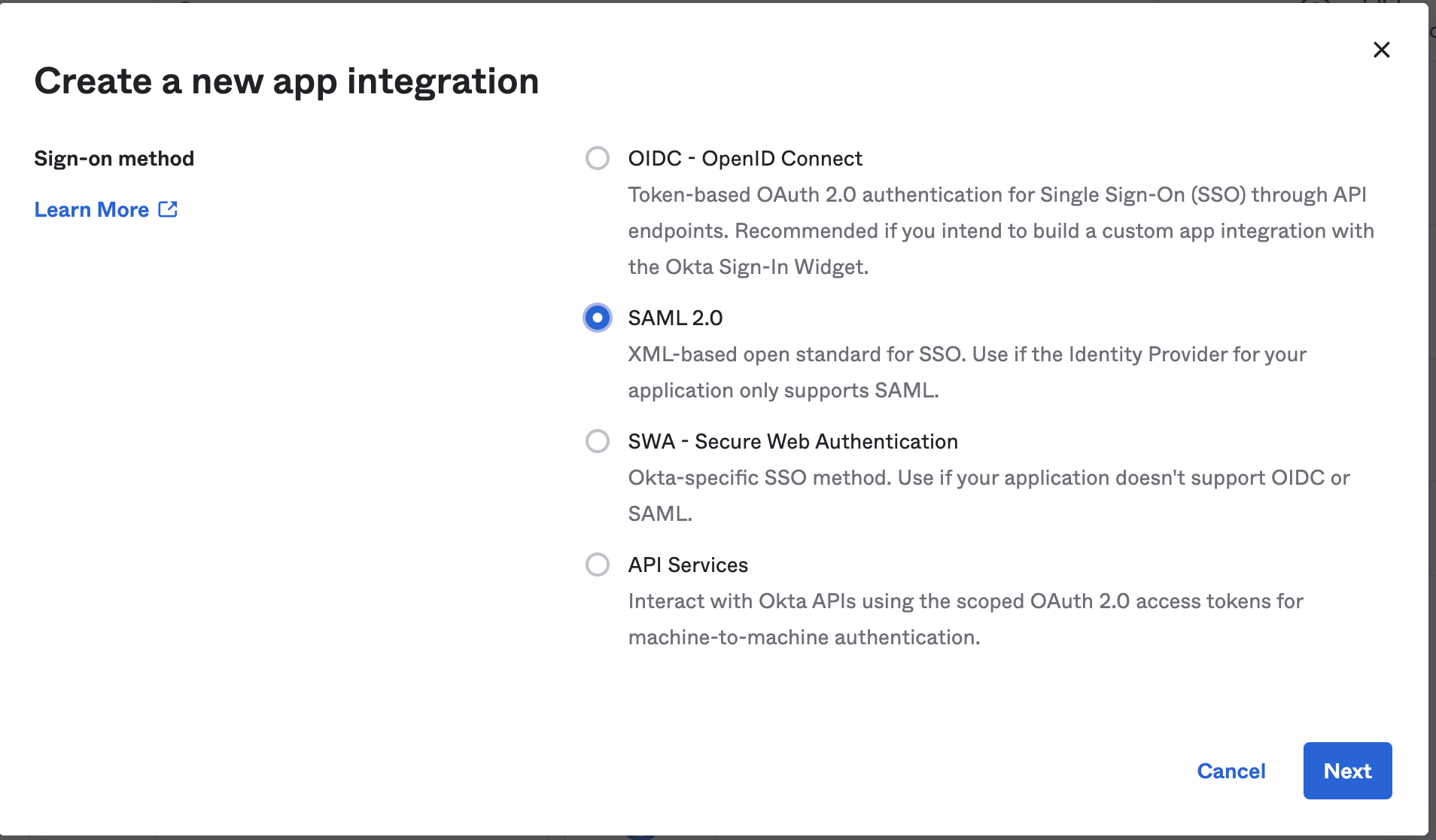
Make sure you select the SAML 2.0 option as the “Sign-on method” and then click “Next”.
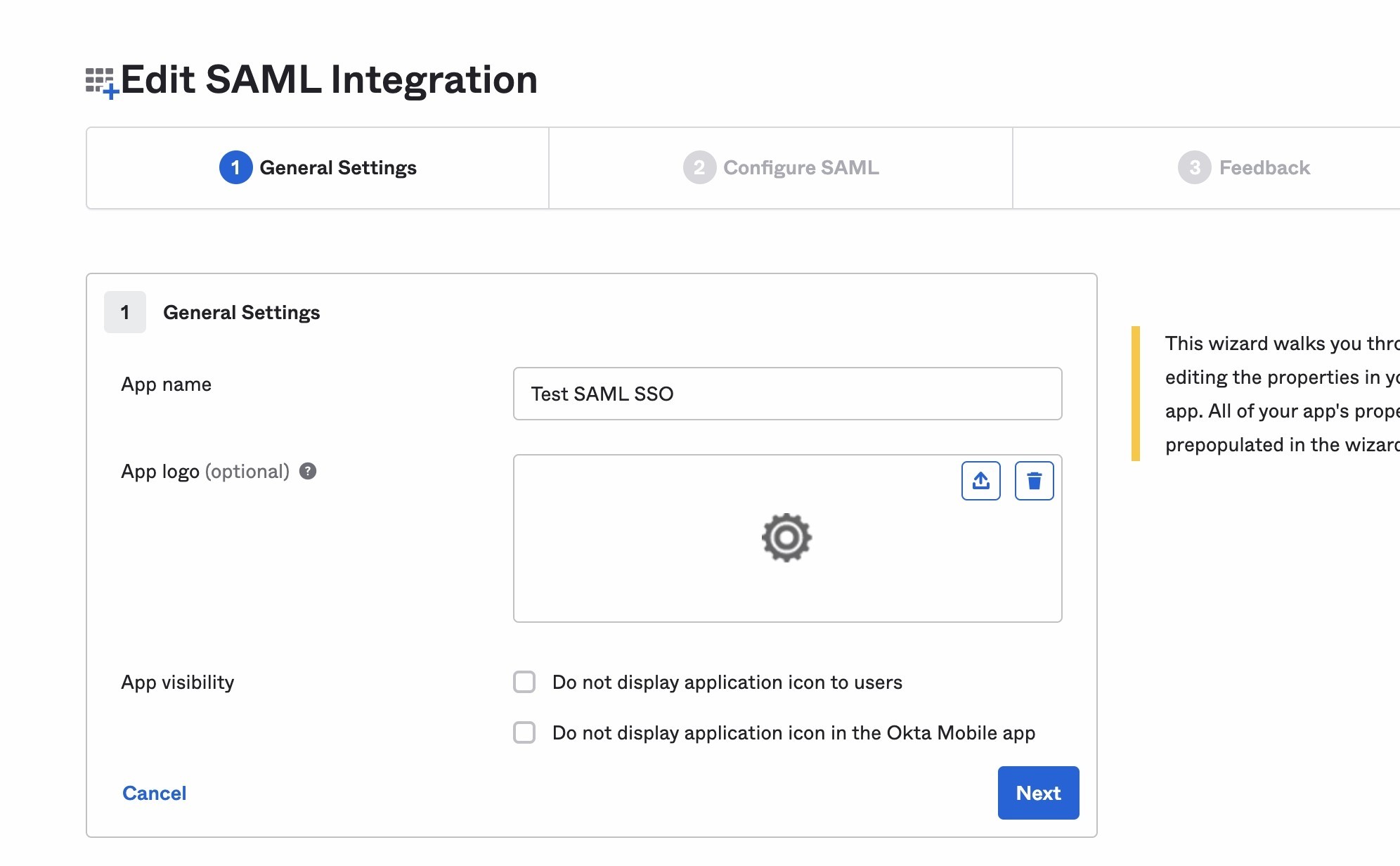
Enter in and select the various options under the General Settings tab as you’d like and then click “Next”.
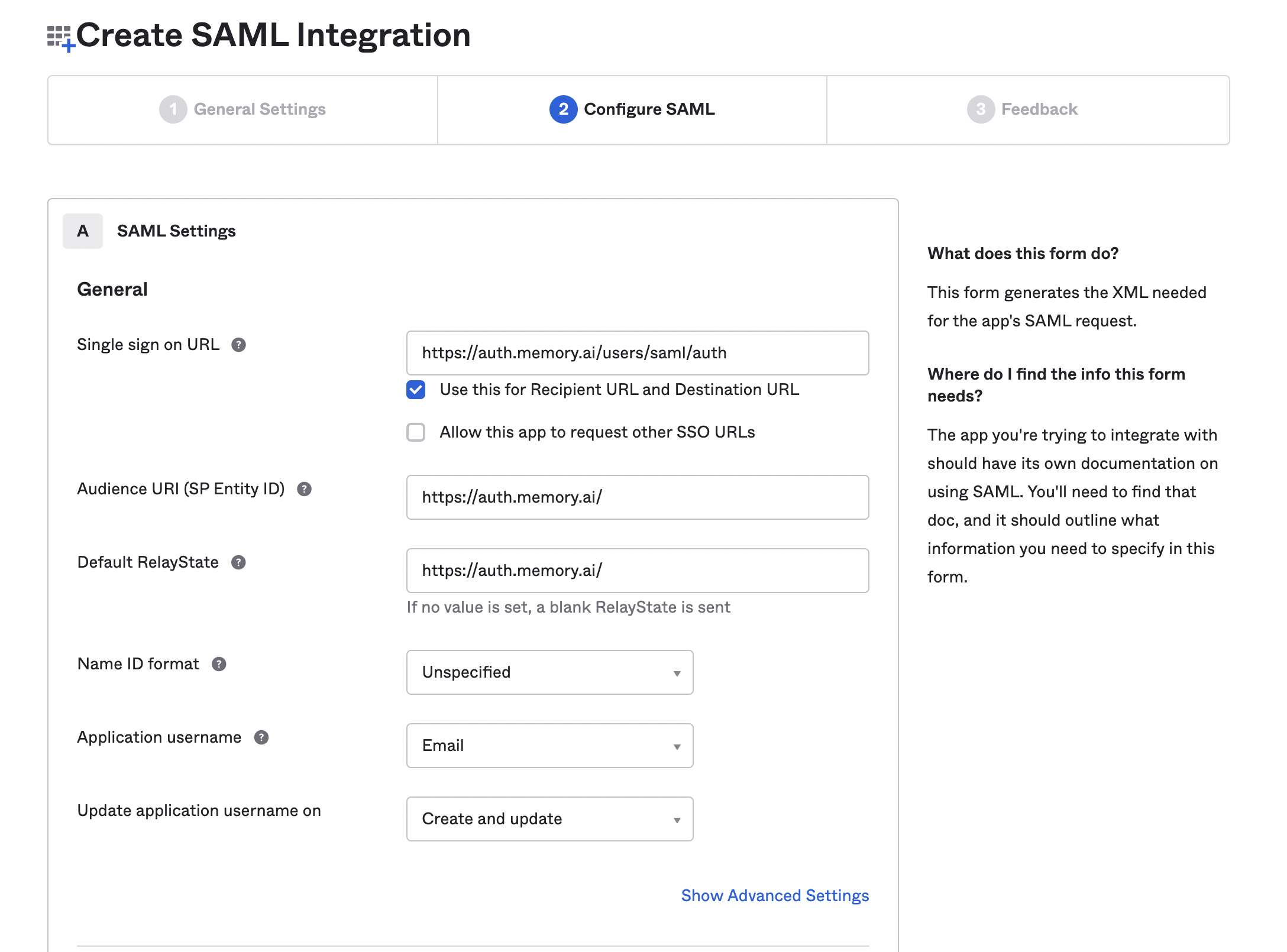
Enter the following attributes under SAML Settings:
- Single sign on URL:
https://auth.memory.ai/users/saml/auth - Audience URI:
https://auth.memory.ai/ - Default RelayState:
https://auth.memory.ai/ - Name ID format: Unspecified
- Application Username: Email
Scroll down and enter the following Attribute Statements:
| Name | Name format | Value |
|---|---|---|
| firstName | Unspecified | user.firstName |
| emailAddress | Unspecified | user.email |
| employeeNumber | Unspecified | user.login |
| lastName | Unspecified | user.lastName |
Once you’ve entered all your Attribute Statements, scroll down to the very bottom and click the “Next” button to finalize this new SSO app.
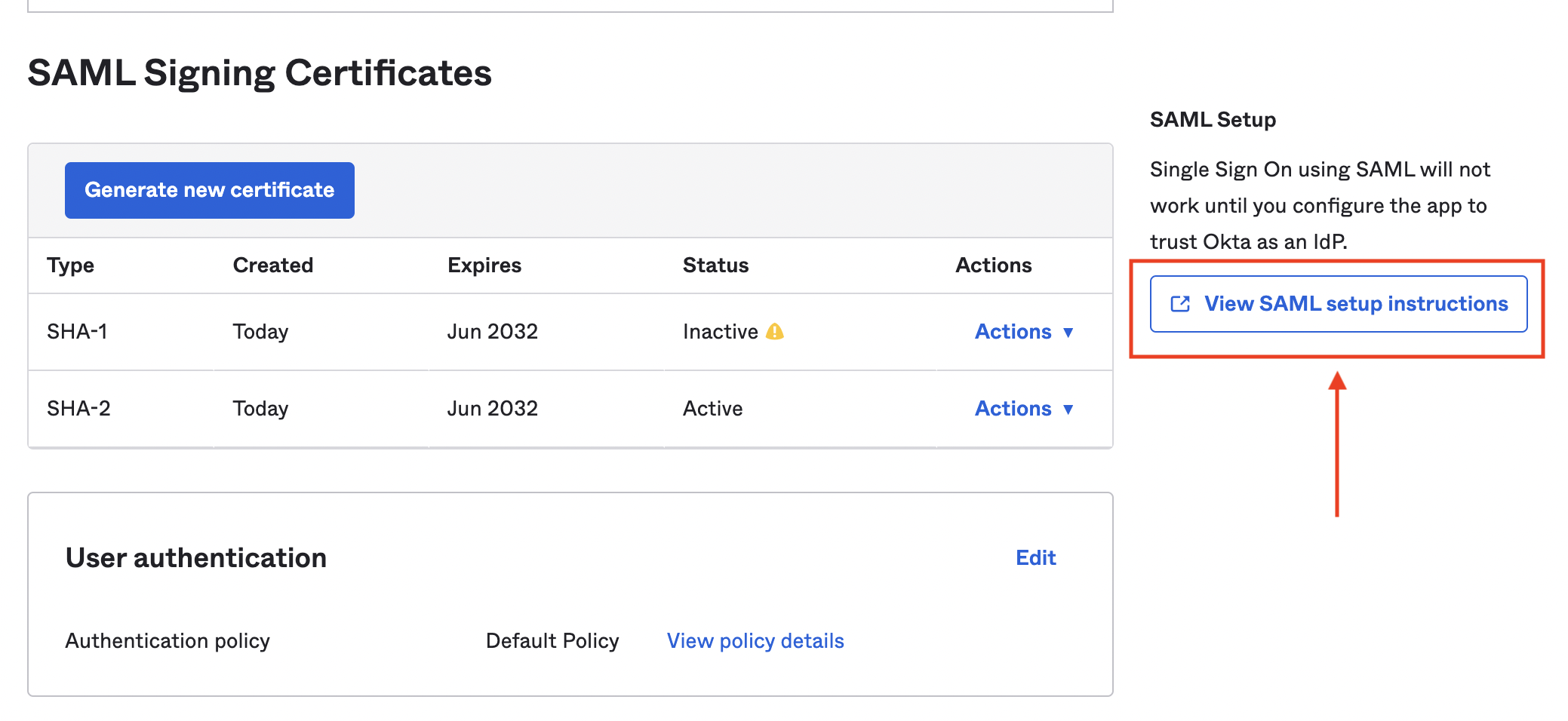
Now you’ll need to access that newly created SSO app in Okta. Click the Applications drop-down from the sidebar, then click Applications. Click your new SSO app and then the “Sign on” header along the top.
Scroll down to the very bottom and click the “View SAML setup instructions” button.
A new tab should open with configuration information you’ll need to share with Timely. Copy the full text from the “Identity Provider Single Sign-On URL” and “Identity Provider Issuer” fields.
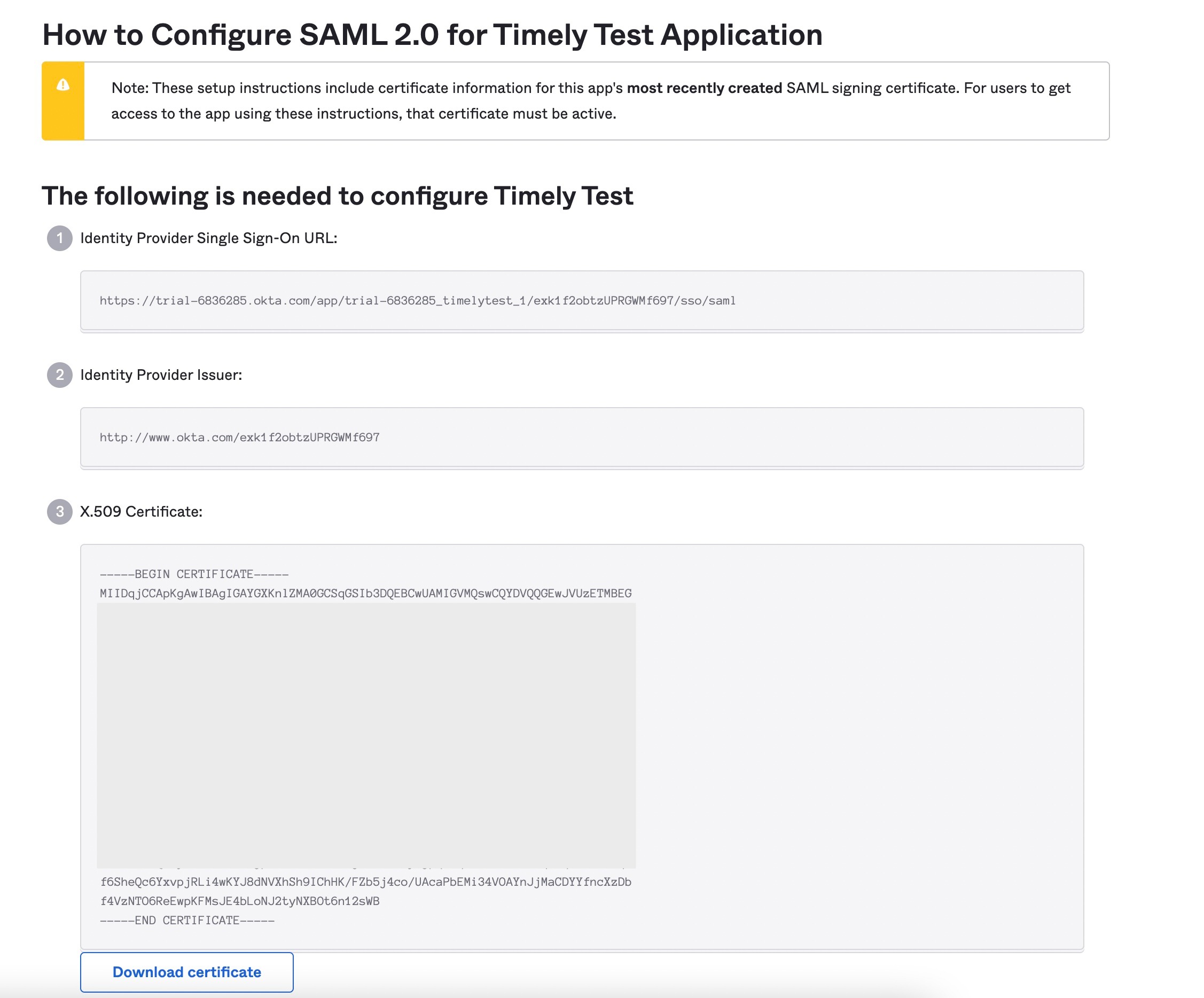
Finally, click the “Download certificate” button at the very bottom. This will create an “Okta.cert” file in your downloads folder.
Completing setup
You’re all set! Contact the Support Team at Timely by emailing us at [email protected] to finalize the integration.
In that email, please include:
- The full text of the “Identity Provider Single Sign-On URL” field
- The full text of the “Identity Provider Issuer” field
- The “okta.cert” file downloaded from the last step
- A list of the email domains in use by your organization (e.g. “@organization.com” or “@companyname.org”)
We’ll circle back to let you know once everything has been confirmed and enabled on our end!
Last updated April 1, 2026
Have feedback for this article or need more help? Contact us now.